- Articles
- Free anti-spoofing tech just made your Office...
Table of Contents
Businesses that subscribe to the Office 365 cloud productivity suite just gained a nice boost in their cybersecurity posture—for free. Microsoft announced that they extended some of the enhanced anti-spoofing capabilities for emails sent and received through their cloud-based Exchange Online Protection (EOP) service. In the most basic of terms, spoofing is when a hacker takes control of a well-known “safe” email address to use for nefarious reasons. Previously available only to those organizations with the most expensive Enterprise E5 plans or for those paying for the Advanced Threat Protection (ATP) add-on, these anti-spoofing features will now help protect all organizations using Office 365.
But when new features for any software as a service (SaaS) are rolled out, there are always some questions that arise. The top three questions Amaxra consultants anticipate most Office 365 customers will ask are:
- How does this “trickle-down cybersecurity” affect your business processes?
- Do existing E5/ATP customers (where this feature was previously enabled) get anything more for their investment?
- If you had previously disabled enhanced anti-spoofing as part of your organization’s anti-phishing policy, is Microsoft going to automatically turn on this feature in your email and potentially cause incompatibilities?
While all businesses are unique, the majority of organizations will want answers to these three questions to maximize their efficiency with the new anti-spoofing capabilities available to their corporate email. Let’s answer each of them in the order we listed above:
You get a safer (but customizable) email experience
It is no secret that most small to midsized businesses (SMBs) choose the Office 365 For Business plans over the Enterprise plans. From a price-performance standpoint, SMBs are willing to sacrifice the cybersecurity features in the more expensive high-end Enterprise plans. However, because more hackers are targeting so-called soft targets in the SMBs space, it made sense for Microsoft to bring some of those Enterprise-grade cybersecurity features to the lower-tier Business plans.
This new enhanced anti-spoofing functionality will now appear in your Office 365 Admin panel. The anti-spoofing features leverage cloud intelligence, sender reputation and patterns to automatically identify potentially malicious domain spoofing attempts made by hackers against your organization. The features are not enabled by default and have to be turned on by your Office 365 Admin. But once this feature is enabled, messages that fail the cloud-powered authentication checks will be automatically sent to the junk mail folder. The most obvious way you’ll know the new anti-spoofing features are working is that your employees will see a lot more email going into their junk folder. This is by design and means you’re anti-spoofing filter is catching more potentially-malicious email. You can use policies to customize the anti-spoofing to best fit your organization’s security needs.
Existing E5/ATP customers get enhanced protection
Just because Microsoft pulled the anti-spoofing technology down from the E5 plans to the lower-priced subscription tiers doesn’t mean they forgot about their top-tier customers. For those current E5 customers, Microsoft will roll out additional updates that improve the anti-spoofing filter beyond its already-advanced capabilities. Enterprise customers will soon have access to deep analytics that provide greater visibility into email spoofing attempts against your organization. This is most useful for enterprise customers who typically have dedicated IT security resources to sift through this data to gain custom insights on the most effective ways to combat hackers.
If you like your anti-spoofing policy, you can (sort of) keep it
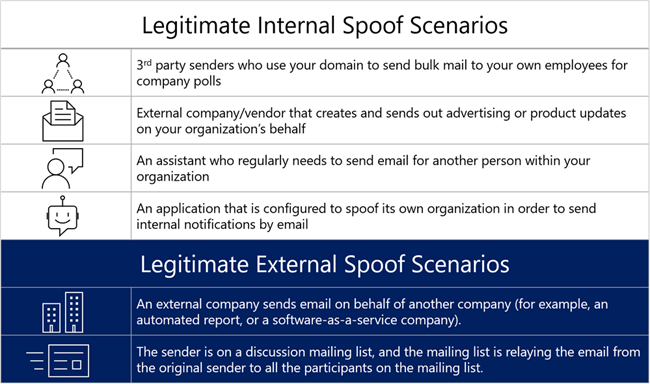
All IT admins hate any kind of SaaS feature update. They live with the constant fear of “What if it breaks [insert name of business-critical software application]?” Some organizations with E5 plans may have disabled anti-spoofing or set specific policies about spoofed emails because there are scenarios when email is legitimately spoofed and should be delivered such as:
So, if your organization needs to disable enhanced anti-spoofing functionality, you will need to set polices before September 21, 2018. After September 21, Microsoft will begin rolling this feature out worldwide, and will enforce the available settings.
IT admins can update the policies allowing known-good and blocked domains for spoofing using PowerShell commands. For example, IT admins can access the settings using the Get/set-Antiphishpolicy command. From there, the Get/Set-PhishFilterPolicy command allows you to set domains that are allowed to send spoofed mails. The Get/Set-AntiphishPolicy command enables you to modify the policies applied to spoofed messages. Because not everyone is comfortable using PowerShell, these policy options are also available in the Security and Compliance center (under Threat Management->Policy->Anti-Phishing).
The Security and Compliance Center is also where IT admins can review internal and external domains being spoofed and sending emails into their organization. This is important because emails from unauthorized senders or domains are treated as spam by Office 365. You can tweak these settings to customize and enhance the spoof protection for your organization.
Enhanced cybersecurity for free is never a bad thing. But as you can tell, it can be complex to administer and manage on your own. Amaxra consultants have decades of combined expertise in deploying and managing cloud-powered Microsoft 365 solutions. If you have your email through Office 365 and want to know how to configure these new anti-spoofing features for your business, then contact us. We can help even if you don’t currently buy your Office 365 licenses from Amaxra.
