- Articles
- How to set up multi-factor authentication and...
Table of Contents
Modern, productive people live in an always-connected, multi-device, and multi-platform world. You probably use an iMac desktop or HP laptop when you are in your office. When you’re at the airport or watching your child’s soccer game, you’re periodically checking work emails from smartphone. And you likely have documents and emails stored in the cloud so that your work is accessible across all these devices and platforms. But the old “enter your user name and password” method of securing these new cloud-based accounts is failing. This failed security method is the primary reason for the dire numbers of recent hacks where passwords were stolen from Equifax (143 million users), Marriott (500 million) and Yahoo (almost 3 billion—yes, that’s billion with a “b”).
Cyber-criminals know we all have too many passwords to remember and we all tend to reuse passwords across multiple accounts. However, for organizations using Microsoft 365 and the Office 365 apps that come with it have a powerful new option to secure accounts across all devices and platforms: Multi-factor authentication (MFA).
The idea of multi-factor authentication is not new. In the bygone era before Netflix (written on historical wiki pages as “1992 B.N.”), people watched movies in their homes on physical media rented from retail stores. The movies on physical media were a costly capital expense for the retailer, so the retailer generated profit from many customers paying a few dollars to rent the physical media for a day or two. To protect the retailer against an unscrupulous customer from not returning that valuable physical media, the retailer required customers to provide the store with two or more forms of identification to authenticate customer accounts with the retailer. Fast forward to our modern cloud-first world, where an online account with multi-factor authentication is more secure than just relying on an ID and password. That’s because adding a second or third factor compensates for the weakness of that one single authentication factor.

More factors = more security for users
It is important to allow more than just one authentication factor for your users. This is so everyone in your organization has access to an alternate MFA option in case their primary option is unavailable. Amaxra has deployed Microsoft 365 and Office 365 with MFA to numerous organizations over years using the following methods:
- Push notification through a mobile app – A push notification is sent to the Microsoft Authenticator app (available on Apple iOS, Google Android, and Microsoft Windows) on a user’s device. The user views the notification and hits the “Approve” link to complete verification. Push notifications through a mobile app provide the least intrusive option for users. Overall, a push notification is often the most reliable and secure option for authentication unless you are traveling to China. For various reasons, China blocks this method on Android phones, which is a perfect real-world example for why you should always have multiple authentication options for your users.
- Generate a verification code in the mobile app – Amaxra often sets up this option for our customers because it’s not only the simplest verification method, it also avoids text or call charges for the user. This method requires users to download and install the Microsoft Authenticator app to their mobile device, which then generates a new secure verification code every 30 seconds. The user enters the verification code into the sign-in interface. While the Microsoft Authenticator app works best if you’re connected to the internet, a data plan is not required to get an MFA code on your mobile device. This is because mobile devices (and most PCs and Macs) keep time by periodically synchronizing their internal clocks with an online “time server” based on an atomic clock. For this reason, you should never turn off the time synchronization feature of whatever device runs your Microsoft Authenticator app.
- Voice call to a phone – In this method, an automated voice call from Microsoft is placed to the user. The user answers the call and presses the # key on the phone keypad to approve their authentication. Call to phone is a great backup method for notification or verification code from a mobile app if the user cannot receive SMS texts on their phone.
- Send a text to a phone – A text message that contains a verification code is sent to the user in this method. The user is prompted to enter the verification code into the sign-in interface.
While these methods are specific to Microsoft 365 and Office 365, most providers of cloud-centric tools for business have multi-factor authentication options for securing user accounts. However, in some cases they are only available as a premium option and often are not turned on by default. Microsoft 365 For Business subscribers get a free version of MFA in the cloud called “Azure multi-factor authentication.” It is a full featured and highly configurable MFA option, but is not enabled for all Microsoft 365 users by default. While Amaxra configures all of our own customers’ Microsoft 365 deployments for multi-factor authentication, we are sharing the basic steps of how to do it if you want to turn on MFA for your organization.
Set up multi-factor authentication in the Microsoft 365 admin center
You can enable MFA for users of Office 365, Microsoft Teams, SharePoint, and all other apps in the Microsoft 365 suite from the cloud-based admin center. Setting up MFA can be done in just a few minutes using these five easy steps:
- In the admin center, go to Users > Active users.
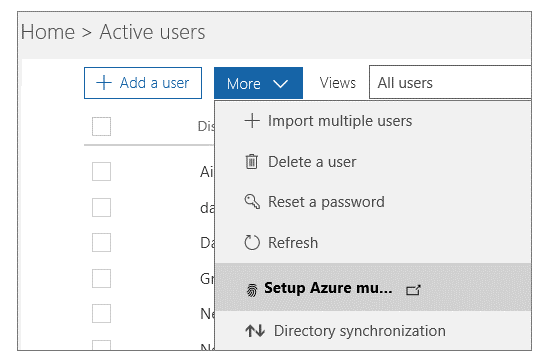
- Click More (…) > Setup Azure multi-factor authentication. In the classic version of the Microsoft 365 admin panel, this option is located at:
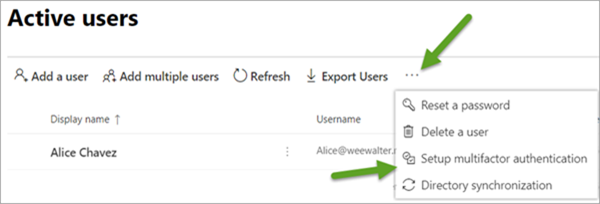
For the adventurous types who use the “preview” version of the admin center, you can find the option for MFA at:
Important If you don’t see the More (…) option, then you aren’t a global admin for your subscription. Contact your organization’s global admin to complete the process for you.
- Find the people for whom you want to enable MFA. In order to see everyone, you might need to change the Multi-Factor Auth status view at the top. The views have the following values, based on the existing MFA state of the users:
- Any – Displays all users. This is the default state.
- Enabled – The person has been enrolled in MFA, but has not completed the registration process. They will be prompted to complete the process the next time they sign in.
- Enforced – The person may or may not have completed registration. If they have completed the registration process, then they are using MFA. Otherwise, they will be prompted to complete the process the next time they sign in.
- Select the check box next to the people you want to use multi-factor authentication. On the right, under quick steps, choose the Enable option.
- In the dialog box that opens, choose enable multi-factor auth.
Once you’ve set up MFA for your users in the Microsoft 365 admin center, you’ll need to send everyone an email giving detailed instructions on how to sign into their cloud accounts with additional authentication—especially if you want them to use any of the methods that use the Microsoft Authenticator app.
Ongoing security for your organization with MFA
This easy five-step method is perfect for small businesses with relatively few users and can be completed in an afternoon. If your organization has over 50 users, then you’ll want to leverage a Microsoft Gold Partner like Amaxra to help configure your MFA. In addition, Amaxra cybersecurity experts can help your employees reduce their exposure to cyberattacks with online training and 24/7 monitoring of your corporate network.
