- Articles
- Enable simple and secure B2B collaboration us...
Table of Contents
With few exceptions, businesses in today’s market require relationships with outside vendors to be successful. The business-to-business (B2B) commerce between vendors in our cloud-connected world does have advantages when it comes to speed and scale. However, security is always a concern. While no good cyber-security professional ever wants to grant external vendors access to an organization’s cloud-based data, the fact is that B2B commerce requires it. But businesses invested in Microsoft 365 productivity solutions with Azure Active Directory (AD) now have a simple way to enable B2B collaboration using a feature called cross-tenant access.
What’s a Microsoft Azure AD tenant for Microsoft 365?
An Azure AD tenant is the dedicated cloud-native user and identity management database provided by Microsoft when a business signs up for Microsoft 365 and other Microsoft cloud services. For businesses with Microsoft 365 and Microsoft Teams, the Azure AD tenant acts as a centralized secure cloud storage of all the corporate users and their unique identity information. So, when an employee signs into Microsoft Teams on their internet-connected device, their corporate identity and login information is checked using Azure AD.
Each Azure AD tenant is distinct and separate from other Azure AD tenants, meaning that every company using Microsoft 365 apps has its own tenant global unique identifier (GUID) number. As an added advantage, Azure AD can be used beyond just Microsoft 365 and Teams to also provide identity and access management to even non-Microsoft cloud applications and services.
Azure AD’s security benefit (and surprising disadvantage for B2B collaboration)
The security benefit of every business having their own Azure AD tenant GUID is obvious: only your authorized company employees can access your company’s apps, data, and other digital assets. However, this walled-garden security setup also creates confusion for some companies invested in the Microsoft 365 ecosystem attempting to engage in B2B commerce.
Say your company is owned by a private equity (PE) firm, that also owns several other companies. One of the other companies owned by the PE firm wants to engage in some B2B commerce with your company and needs to share various documents and data files using Microsoft SharePoint and collaborate in real time using Microsoft Teams. Although all the various companies owned by the PE firm operate independently of each other, the PE firm ensured that all companies under their ownership use Microsoft 365 productivity apps. However, even though both companies have nearly-identical Microsoft 365 setups, their two unique Azure AD tenants would require the IT departments at each company to set up extranets, authorize specific users, and often those users’ multi-factor authentication (or MFA, which Amaxra recommends everyone should use to enhance your business’ security) schemes become annoyingly “doubled up” in the process—forcing the external users at each company to sign in and verify their identities twice just to look at a cloud-based Excel spreadsheet or chat on Teams.
How cross-tenant access with Azure AD simplifies B2B collaboration
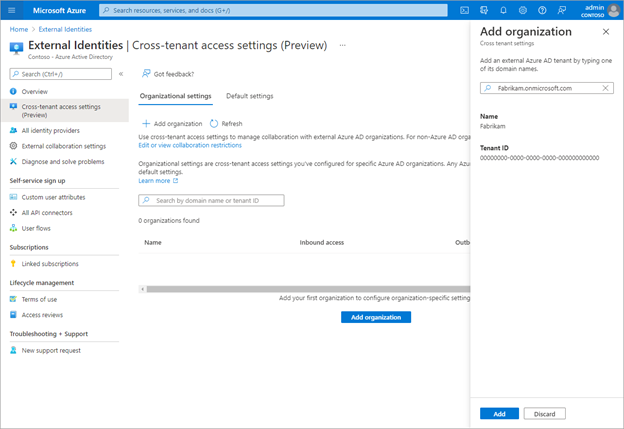
To simplify B2B collaboration between two separate Azure AD tenants, Microsoft is providing a comprehensive set of External Identities settings. IT managers can use these cross-tenant access settings to manage how they securely collaborate with other Azure AD organizations.
When engaging in B2B collaboration, these cross-tenant access settings provide granular control over how an external Azure AD tenant collaborate with you (inbound access) and how your users collaborate with the external Azure AD tenant (outbound access). These settings help Azure AD-enabled businesses to manage inbound and outbound B2B collaboration and scope access to specific users, groups, and applications. Cross-tenant settings can get very granular in terms of limiting who can invite external users, allowing or blocking B2B-specific domains, and setting restrictions on guest user access to your company’s directory. It can also let your company trust the MFA from other Azure AD tenants, ensuring that users who have already completed MFA in their home tenants won’t have to complete MFA again in your tenant again.
Amaxra helps businesses set up external identities for cross-tenant access
Any IT manager with either “global admin” or “security admin” access to your company’s Azure portal can set up cross-tenant access in the Azure Active Directory>External Identities menu. However, entering in the Azure AD tenant GUID for your external B2B vendor into this menu is just the first of many steps to success. Note that changing the default inbound and outbound settings could potentially block access to existing business-critical apps on both yours and your B2B partner’s organizations.
Rather than do it yourself, connect with an Amaxra consultant. As a Gold-level Microsoft Partner firm with over a decade of experience deploying Microsoft cloud solutions for small-to-midsized businesses, Amaxra consultants are experts in Microsoft 365 and Azure AD. Our consultants will assess your needs and help you identify what resources users in both Azure AD tenants need to access and help configure your settings for optimal performance and security.
